In today’s increasingly digital landscape, cybersecurity is a critical concern for individuals, businesses, and governments. As technology advances, so do the threats targeting sensitive data, systems, and networks. To counter these threats, establishing clear cybersecurity goals is essential. This guide explores the primary goals of cybersecurity and their significance in safeguarding digital assets.
1. What is Cybersecurity?
Cybersecurity refers to the practice of protecting systems, networks, and data from digital attacks, theft, and damage. It encompasses various technologies, processes, and best practices designed to counter evolving threats.
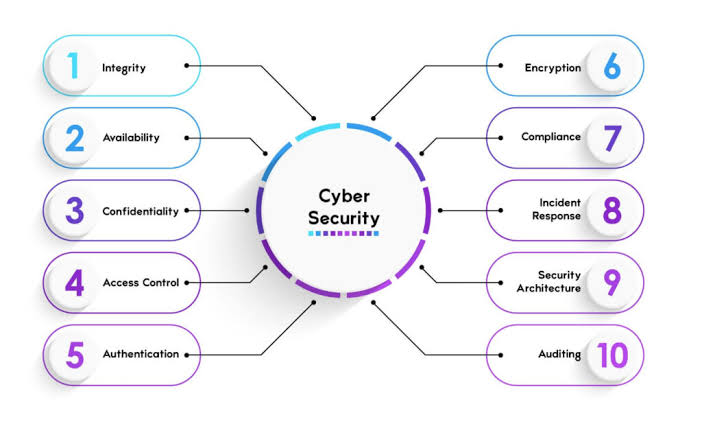
The primary objectives of cybersecurity, often referred to as the CIA Triad, include confidentiality, integrity, and availability. Beyond this, modern cybersecurity efforts focus on accountability, authentication, and resilience.
2. Key Cybersecurity Goals
a. Confidentiality
Confidentiality ensures that sensitive information is accessible only to authorized users. This goal prevents unauthorized access, ensuring that personal, corporate, or government data remains private.
- Examples: Encrypting emails, using secure passwords, and implementing access controls.
- Challenges: Insider threats and sophisticated hacking methods like phishing can compromise confidentiality.
b. Integrity
Integrity ensures that data remains accurate, consistent, and unaltered during storage or transmission. Any unauthorized modifications must be detected and addressed promptly.
- Examples: Using checksums, digital signatures, and secure communication protocols.
- Challenges: Cyberattacks such as data breaches or malware can compromise data integrity, leading to misinformation and operational disruptions.
c. Availability
Availability ensures that systems, networks, and data are accessible when needed by authorized users.
Downtime can lead to financial losses and reputational damage, making this goal vital.
- Examples: Implementing redundancy, regular backups, and robust disaster recovery plans.
- Challenges: Distributed Denial of Service (DDoS) attacks and natural disasters can disrupt availability.
d. Accountability
Accountability ensures that actions performed on a system can be traced back to specific individuals or entities. This deters malicious activities and supports forensic investigations.
- Examples: Audit trails, activity logging, and monitoring tools.
- Challenges: Sophisticated hackers may manipulate logs to obscure their actions.
e. Authentication
Authentication verifies the identity of users, systems, and devices. It ensures that only legitimate entities can access sensitive resources.
- Examples: Two-factor authentication (2FA), biometric verification, and cryptographic certificates.
- Challenges: Weak or stolen credentials remain a major vulnerability in cybersecurity.
f. Resilience
Resilience focuses on a system’s ability to recover from cyberattacks or disruptions. It ensures that operations can continue with minimal impact, even under adverse conditions.
- Examples: Incident response plans, cybersecurity drills, and threat intelligence sharing.
- Challenges: Evolving threats and resource constraints can make resilience difficult to achieve.
3. Importance of Cybersecurity Goals
a. Protecting Sensitive Information
Cybersecurity goals ensure that sensitive information, such as financial data or medical records, remains secure from unauthorized access or misuse.
b. Ensuring Business Continuity
A robust cybersecurity framework prevents operational disruptions caused by cyberattacks, ensuring uninterrupted services and customer satisfaction.
c. Compliance with Regulations
Meeting cybersecurity goals helps organizations comply with laws like GDPR, HIPAA, and PCI DSS, avoiding legal penalties and safeguarding reputation.
d. Building Trust
Customers, partners, and stakeholders are more likely to trust entities that demonstrate strong cybersecurity practices, enhancing long-term relationships.
4. Strategies to Achieve Cybersecurity Goals
a. Conduct Risk Assessments
Identify vulnerabilities and assess potential threats to prioritize resources and enhance protection.
b. Implement Multi-Layered Security
Use a combination of firewalls, intrusion detection systems, encryption, and access controls to secure systems and networks.
c. Promote Security Awareness
Educate employees and users about cybersecurity best practices to reduce human error and prevent breaches.
d. Regular Updates and Patching
Keep software and systems updated to address known vulnerabilities and minimize risks.
e. Develop an Incident Response Plan
Establish a clear protocol for detecting, responding to, and recovering from cyber incidents.
f. Leverage Artificial Intelligence (AI)
Use AI-powered tools to detect anomalies, prevent threats, and enhance response times.
5. The Future of Cybersecurity
As technology evolves, so do cyber threats. Cybersecurity goals must adapt to address emerging challenges like quantum computing risks, IoT vulnerabilities, and AI-driven attacks.

Collaborative efforts between governments, organizations, and individuals are essential for a secure digital future. Investments in advanced technologies, such as machine learning and blockchain, will further strengthen defenses.
Conclusion
Cybersecurity goals serve as the foundation for protecting digital assets in an interconnected world. By prioritizing confidentiality, integrity, availability, accountability, authentication, and resilience, individuals and organizations can mitigate risks and thrive in a secure digital environment.
Investing in robust cybersecurity practices today ensures a safer, more reliable tomorrow.
“This Content Sponsored by Buymote Shopping app
BuyMote E-Shopping Application is One of the Online Shopping App
Now Available on Play Store & App Store (Buymote E-Shopping)
Click Below Link and Install Application: https://buymote.shop/links/0f5993744a9213079a6b53e8
Sponsor Content: #buymote #buymoteeshopping #buymoteonline #buymoteshopping #buymoteapplication”